Played 0xfun CTF with my team THEM?!. This time 0xfun were hosting, so we went head to head with them. Got a lot of solves and secured 2 first bloods OSINT & Forensics. Have fun reading the writeups see you in the second edition! --- #### Rev — pingpong Write-up ## 📎 Attachments [pingpong](/atta
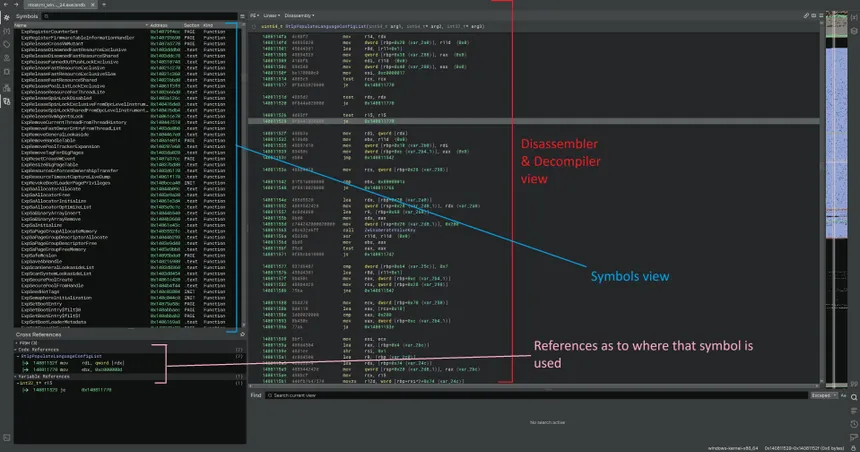
Win Kernel Modulo Reversing #1
Here’s something interesting I’ve been learning about lately. I’m still far from mastering it Windows kernel-mode reversing is honestly an ocean lmao. The deeper you go, the more you realize how much there is left to explore. This post is just a snapshot of what I’ve discovered so far while diving i
0xL4ughCTF v5 - Invisible Ink
I played 0xL4ugh CTF V5 with my team THEM?!. I wasn’t very active during the competition, but I still solved three challenges, including this one. It was an amazing CTF with creative challenges, and I’m really looking forward to the next 0xL4ugh CTF v6 edition ## 1) 0xL4ugh CTF V5 — Invisible Ink

IDEHv7 CTF Writeups
IDEH is a Moroccan CTF competition hosted by INPT. During this event, I solved many challenges while playing solo **lmao**, and it was an amazing experience overall. The competition was intense, fun, and full of learning opportunities. I also had the chance to meet and connect with many great people

NexusCTF writeup
This challenge was first-blooded and only solved by me during the entire competition , if you’re a reverse engineering enthusiast, this blog is for you. Let’s dive in and break down the reversing process step by step , have fun, See you next year at NexHuntCTF --- ## 📎 Attachments [eleonoras](/a

FlagY reversing Writeup
FlagYard is a competitive CTF platform that hosts a wide variety of challenges across multiple categories, including reverse engineering, cryptography, pwn, forensics, and web. It’s a solid environment to practice real technical skills, face non-trivial problems, and continuously sharpen your cybers



